Many cyber security professionals rely on process and methodology to ensure they are as effective as possible in preventing cyber criminals from succeeding. In the same way, cyber criminals also take a methodological approach to achieving their objectives – what has been referred to as the “cyber kill chain”. Success in cyber security in part comes from understanding their approach and breaking it so it won’t succeed; something Viakoo takes an active role in.
{{cta(‘1b8a057e-606b-4d5f-a804-0a569eb13753′,’justifycenter’)}}
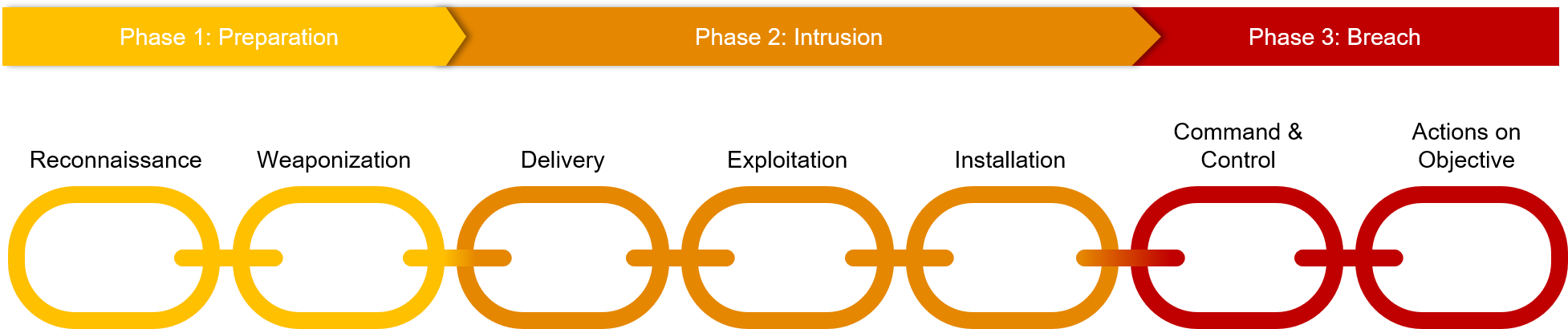
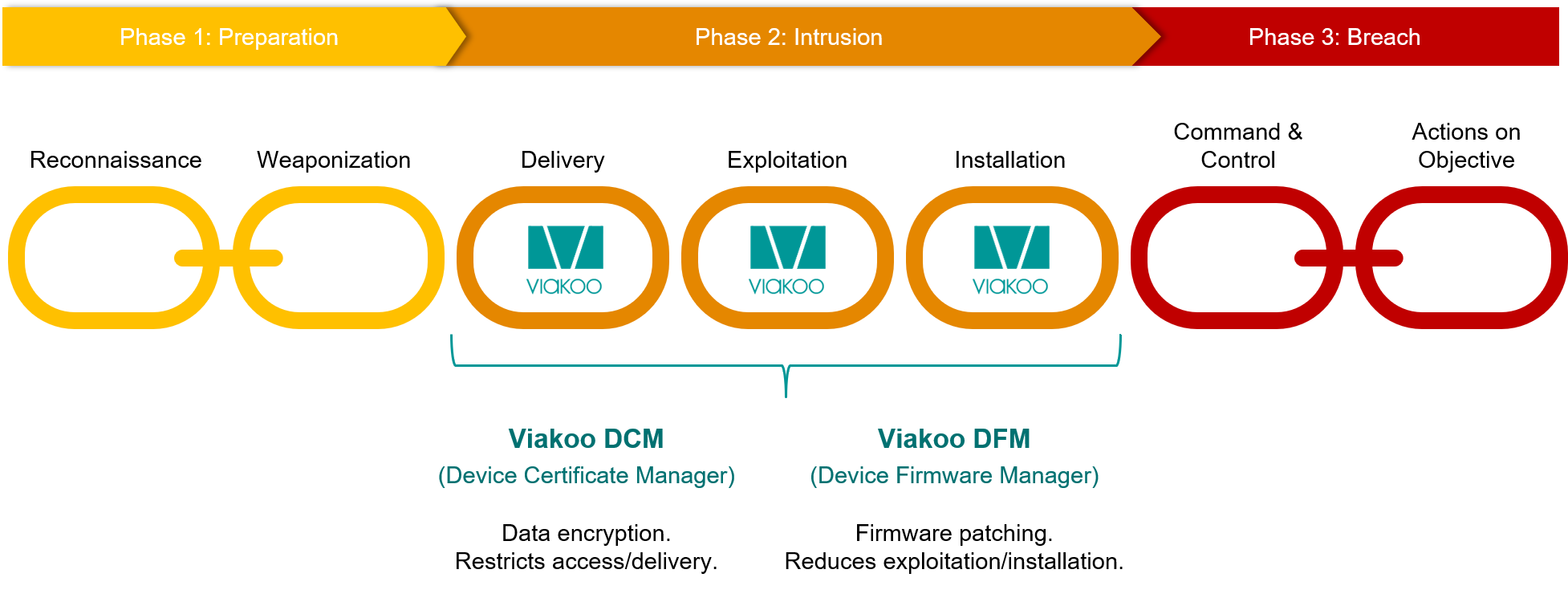
If you are not familiar with the term “kill chain” it’s a military concept of how attacks are structured across multiple phases. In 2011 Lockheed Martin applied this concept to cyber intrusions and created a seven step intrusion kill chain (Fig 1 below), highlighting the steps malevolent actors take both inside a victim’s network and outside of it. Over time this approach has been adapted and extended, and it forms the basis of MITRE’s ATT&CK framework and many others.
In the first phase (Phase 1: Preparation) the attacker performs reconnaissance of their target and analyzes the behavior in order to define the most effective way to achieve their goals. Often this preparation is performed outside of the network, but can take advantage of network weaknesses to perform reconnaissance. A good example of this is the Carbanak hacking group which targets financial institutions, and is estimated to have stolen over $900M from banks. By watching employee movements after gaining control of webcams and other camera devices inside the banks, the hacking group had months to observe and gather information around internal processes and weaknesses. This enables the second step of the preparation phase, weaponization. With the detailed knowledge they’ve acquired, hackers can then develop highly effective cyber threats to exploit the vulnerabilities they’ve found.
In the second phase (Phase 2: Intrusion) cyber criminals take action inside your network, in the form of delivering the cyber weapon, activating it, and installing backdoors and other forms of connecting it to the perpetrators. This phase happens within your network, and this is the phase where your actions can break the kill chain most directly by focusing on vulnerability remediation and cyber hygiene. Keeping devices on the most recent (most secure) version of firmware can close holes that cyber criminals could otherwise exploit. Having all devices using certificates (802.1x, TLS/SSL, OPC-UA, etc) further breaks the chain by ensuring that no rogue devices are being used, and that all traffic between devices is encrypted. And it goes without saying that all devices should never use default or easily-guessed passwords; instead a governance policy around passwords should be enforced with automated device password management. Effective cyber hygiene can also stop lateral movement, thus reducing the potential damage from the cyber threat.
The last phase (Phase 3: Breach) is where cyber criminals have command and control over the operation of the cyber threat, and guide it towards achieving it’s objectives. Similar to the first phase, at this stage the “action” is mostly outside of your network but steps can be taken to reduce the impact. For example, using an automated service assurance solution can track if devices have abnormal traffic patterns that might signal active command and control, or that objectives like exfiltration of data are being achieved.
Summary
While there are many variations of the cyber kill chain, one thing is constant: attacks happen over time and stages, and the earlier the chain is broken the better. With automated vulnerability remediation, cyber hygiene, and service assurance solutions organizations improve their odds of stopping malevolent actors before financial or reputational losses occur. Viakoo is the leader in making unmanaged and IoT devices work securely, and helping you attack the cyber kill chain. Want to take action? Sign up here for a 1:1 demo of Viakoo, and learn how to use automation to stop cyber criminals from exploiting your most vulnerable devices.
Want to learn more on cyber hygiene of your unmanaged & IoT devices? Download your copy of Ten Proven Tips to Secure Unmanaged & IoT Devices:
{{cta(‘9ff2faa6-7984-4884-9644-db33021e0e0c’,’justifycenter’)}}