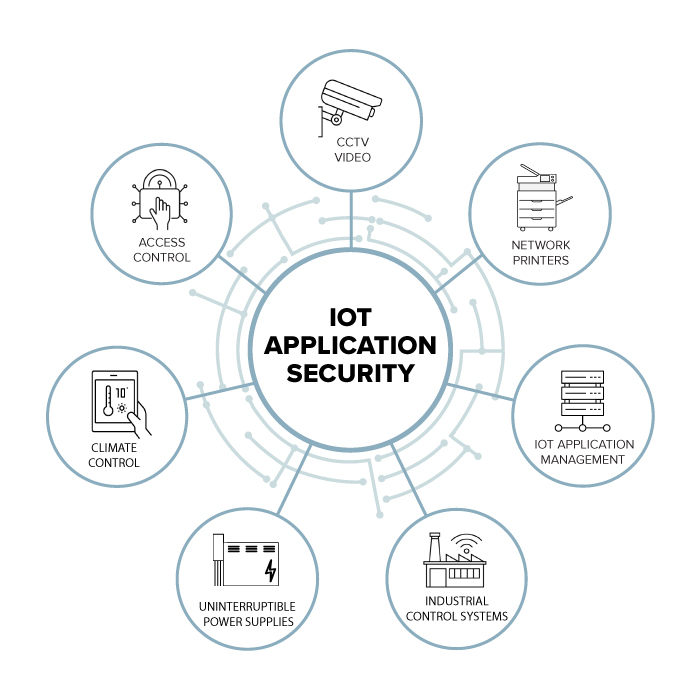
Understanding the IoT Application Security Landscape
In today’s hyper-connected world, IoT Application Security has become integral to optimize business operations and workflows. IoT applications have transformed how we interact with technology, from tightly coupled devices to industrial automation, and healthcare devices, the IoT attack surface has grown exponentially. However, with this hyper-connectivity comes a significant challenge: IoT security. IoT applications and devices are prime targets for cyberattacks, making robust IoT application security a paramount concern for businesses.

Sign up for a demo: Solve the last mile of your IoT Security with Viakoo’s “Application Data Mapping (ADM)”.
- Perform IoT application discovery by analyzing applications and the devices connected to them, yielding high fidelity operational and configuration data about your IoT devices, and application dependencies.
- Viakoo enables organizations to quickly implement an automated, agentless, and repeatable process for finding and remediating IoT application vulnerabilities.
- Day one: start discovering complete device information, and application workflows.
- Enable tool consolidation through tight integration with all leading asset discovery solutions.
eBooks – Solution Briefs – Case Studies
The Future of IoT Application Security
Securing the Internet of Things: Ensuring the Future of IoT Application Security.
he Internet of Things (IoT) has evolved into a transformative force, connecting devices, systems, and people in unimaginable ways. IoT applications have become integral to businesses. From industrial automation video surveillance systems to healthcare, this rapid expansion also brings many security challenges that must be addressed to ensure IoT’s continued success and safety. This article delves into IoT application security, exploring its importance, key challenges, and strategies for safeguarding this interconnected ecosystem.
The Significance of IoT Application Security.
IoT application security refers to the measures and protocols to protect the vast network of IoT devices, data, and interactions. Its significance cannot be overstated:
Data Privacy: IoT applications collect and transmit vast amounts of personal and sensitive data, building user trust and complying with data protection regulations is imperative.
Business Continuity: An IoT cybersecurity breach can disrupt production, logistics, and application services, leading to financial loss.
Safety: In sectors like healthcare and automotive, IoT devices can impact the protection of individuals. Vulnerabilities in these systems can have life-threatening consequences.
Consumer Trust: A single security incident can erode trust and deter users from adopting IoT technologies.
Critical Challenges in IoT Application Security
Securing IoT applications is a complex endeavor, primarily due to the following challenges:
Diverse Ecosystem: IoT encompasses many devices, each with its hardware, software, and communication protocols. This diversity complicates the development of uniform security measures.
Scale: IoT networks often comprise millions of devices, making managing and monitoring difficult.
Resource Constraints: IoT devices need more processing power, memory, and energy resources. Traditional security solutions may need to be more resource intensive.
Interconnectivity: The interconnected nature of IoT devices means that a vulnerability in one device can ripple effect across the entire network.
Legacy Systems: Many existing IoT devices must be designed with security in mind and retrofitting them can be challenging.