IoT Device Security
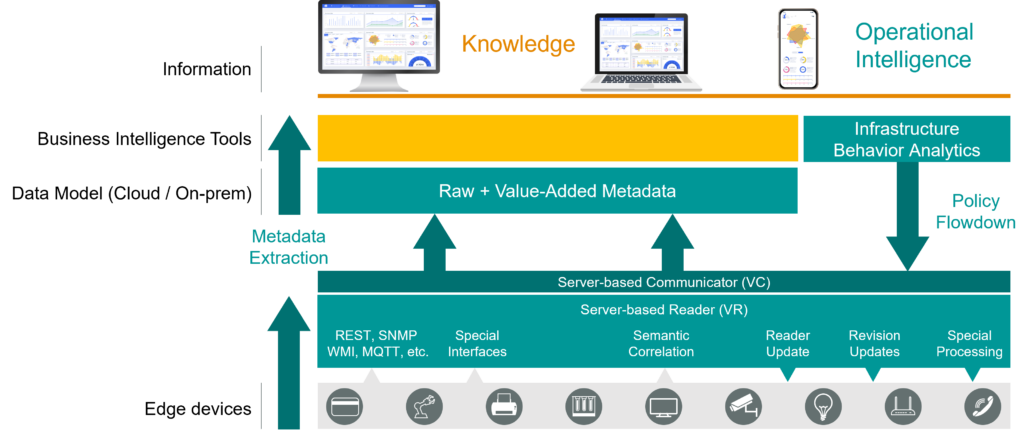
The Viakoo IoT device security platform architecture is agentless and automated, with the ability to span across multiple network topologies. It is secure-by-design, with comprehensive reporting and compliance features, as well as flexible deployment options. It is also interoperable with discovery platforms and threat assessment solutions.
Agentless & automated metadata extraction refers to the ability of the Viakoo IoT device security platform to extract metadata without the need for agents. This is important because it increases the ability to remediate issues, reduce the attack surface, and improves the IoT device security.
The IoT device security platform must be able to span multiple network topologies, including both wired and wireless networks. This is important because it allows the platform to be deployed in a variety of environments and provides flexibility in terms of deployment options. IoT device security platforms must be designed with security in mind from the ground up. This includes features such as encryption, authentication, authorization, and auditing. The Viakoo IoT security platform provides comprehensive reporting and compliance reporting capability.
Key Architectural Features
- Agentless & Automated Metadata Extraction
- Ability to Span Across Multiple Network Topologies
- Secure-by-Design
- Comprehensive Reporting & Compliance Features
- Flexible Deployment Options
- Interoperability with Discovery & Threat Assessment Solutions
Frictionless IoT Device Security Platform
The Viakoo Action Platform has a proven architecture with over 1.2 Billion hours of real-life usage. Below are the key elements of how Viakoo gathers and analyzes data, provides insights into IoT vulnerabilities and operations, and performs automated vulnerability remediation. In addition, Viakoo provides flexible options for deployment and span of control.
Agentless & Automated Metadata Extraction
The Viakoo Action Platform has an agentless mechanism for extracting real-time system metadata, and providing that data for a detailed analysis with the Viakoo’s Reasoning Engine. At no time is production data (such as network traffic, video or audio, or sensor output) used; instead Viakoo captures the IoT device and connected device metadata values on a continuous basis, which is stored in a Digital Twin format.
Unlike discovery solutions that focus on network traffic, Viakoo performs application-based discovery and metadata extraction. This data allows the Viakoo Action Platform to coordinate with the applications that manage their related Tightly Coupled Devices for remediation to a secure state, verifying interoperability, and creating and tracking an audit trail for all actions.
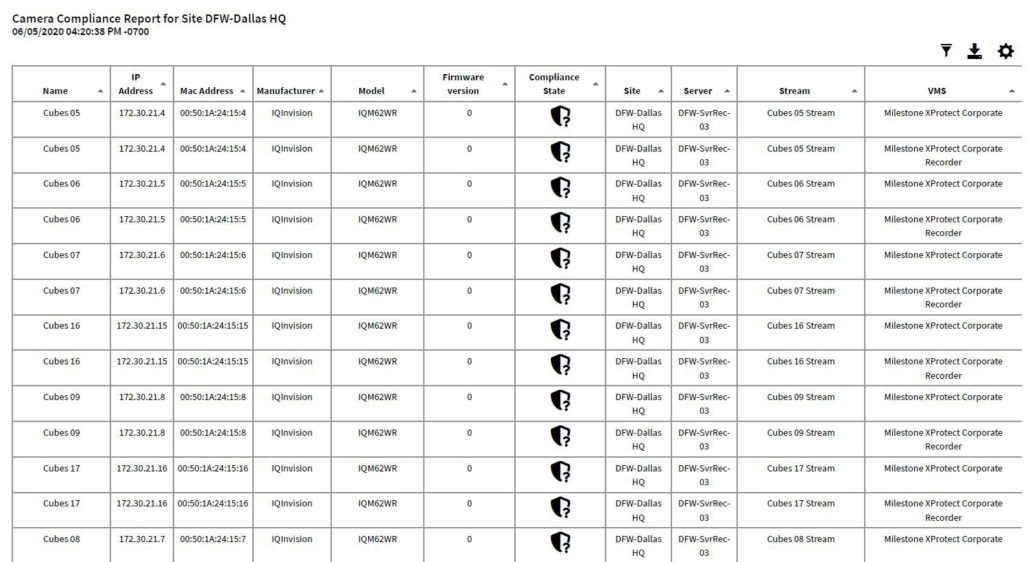
Detailed Device Insights & Compliance/Reporting
Viakoo is based on a Digital Twin model, where the metadata we extract in real-time creates both current and historical views of the production environment. This means you can go back across any time range, location, or type of IoT device and have the actual production data available for reporting and analysis.
The Viakoo Action Platform goes a level deeper to give you reporting on the firmware, password and 802.1x/TLS certificate status for even the most complex enterprise IoT devices supporting zero-trust initiatives. Integrated reporting capabilities allow you to share this information with others within your organization or with auditors.
Remediation Across Multiple Locations and Network Topologies
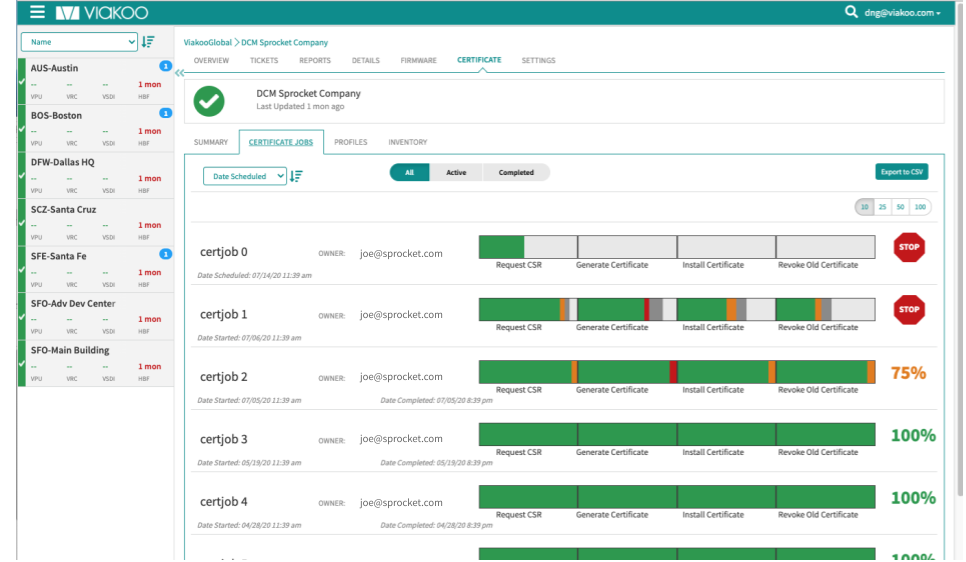
Discovering IoT and cyber security vulnerabilities is is only part of the solution, remediating and re provisioning them into service at scale is quite another. This is where the Viakoo Action Platform shines by enabling you to perform cyber hygiene functions across your entire organization from a centralized location.
Think globally, act locally. Instead of needing people to be physically present at multiple sites and locations, the Viakoo Action platform provides centralized 1 click IoT and cyber vulnerability remediation for firmware, passwords and certificates. This way, you can move to a compliant posture organization-wide almost instantly.
Deployment Options
Viakoo Action Platform helps maintain your compliant risk posture. Viakoo’s user interface takes a compliance-based approach, highlighting which devices are out of compliance and need updating in real-time without agents. Firmware, passwords and certificates can be managed and updated from a single interface. With Viakoo, once was a manual processes subject to human error, will keep your enterprise IoT devices secure reducing your attack surface thus risk 24x7x365.
Learn More About the Viakoo Architecture
Security is built in from the ground up with the Viakoo Action Platform. Our platform is designed so that there is never two-way communication from Viakoo across your network; all we require is a single outbound-only port. All data and device information across the Viakoo Action Platform is encrypted at all points on its journey. And Viakoo is certified by SSAE as SOC-2 Type 2 compliant, the highest standard of security for datacenter operations. Detailed information, including penetration testing and other compliance reports are available on request.
Patented Technology
Until Viakoo, it was very costly to manually track and remediate cyber vulnerabilities across thousands of devices in an unlimited number of locations. Viakoo’s is a patented able to span IT and IoT network topologies, collection and reporting of key metrics, enabling the IoT and cyber risk to be mitigated. For the first time, an IoT security company can centralizes and automates the discovery, remediation and compliance of security for IoT devices. The Viakoo IoT device security platform dramatically reduces the costs associated with enterprise IoT device security, and makes the possible, and cost effective that CISO can finally close IoT device security risks at an ROI far higher than almost any other security project.
Viakoo IoT Security Platform
Contact Viakoo for more information!
Let Viakoo prove the value of the Viakoo IoT Management Platform by reducing costs to manage your device firmware, password compliance, and secure certificate management. Viakoo is a 100% AGENTLESS enterprise scale management solution addressing the IoT cyber security needs of all enterprises.
Viakoo’s IoT Management Solution will scale with your enterprise. With Viakoo, we can prove significant cost reduction, unmatched scalability, a drastic reduction in staffing requirements to manage your devices, and most of all, you will be able to provide an audit trail for compliance that will make any CSO, IT Manager, Risk Manager etc. very happy.
Contact Viakoo for an IoT device risk assessment that will identify your attack surface, today!
Enterprise IoT Device Management & Remediation

IoT Device SSL/TLS Certificate Management
Extend Zero Trust coverage to IoT devices with 802.1x / TLS / OPC-UA automated certificate provisioning and management.
Are Your Enterprise IoT Passwords Compliant
Automate verification of password policies at scale and meet standards compliance such as PCI, NERC, and NIST.

Enterprise IoT Device Firmware Management
IoT device security and management with automated firmware updates at an enterprise scale.