Manage Your IoT Device Firmware
IoT device firmware is the low-level software that runs on a device. It can be thought of as the operating system for the device. IoT devices usually have firmware that is embedded in the hardware. This firmware controls how the device behaves and interacts with other devices and systems such as IP/CCTV cameras, access control systems, printers, APS systems, and many more critical devices.
Importance of IoT Device Firmware Updates
One of the biggest challenges with IoT devices is keeping the firmware up to date.
IoT device firmware updates are often released by manufacturers in response to security vulnerabilities that are discovered. If a device has an outdated or vulnerable firmware, it can be exploited by attackers.
Unfortunately, firmware updates are not always easy to install. In many cases, they must be installed manually. This can be a tedious and time-consuming process, especially for organizations that have deployed devices from multiple vendors, and locations.
This is when the typical enterprise will need an IoT device discovery platform that will provide an accurate view to their connected devices.
Updated firmware for IoT devices will reduce your chances of a cyber attack, thus mitigate risk through remediation.
When firmware updates are not installed in a timely manner, it leaves the organization vulnerable to attack. attackers can exploit known vulnerabilities to gain access to the device or the data it is processing. In some cases, they can even use the device to launch attacks on other systems.
To reduce the risk of attack, it is important for organizations to have a process in place for firmware updates. This process should be designed to ensure that all devices are kept up-to-date with the latest firmware releases.
Respond to IoT cyber security vulnerabilities, by correcting outdated firmware before it becomes an issue.
Every enterprise has had an issue or is prone to a IoT cyber attack. The formula for IoT device security is: Discover – Identify – Remediation – Repatriation.
Keep your IoT device firmware updated on thousands of devices via automatic compliance with the Viakoo Action Platform with Device Firmware Manager (DFM).
Firmware: A key security breach vector
The easiest way for a bad actor to compromise the enterprise is by exploiting out-of-date and vulnerable firmware. Unfortunately, device manufacturers don’t make the firmware update process easy. It’s largely a tedious, manual, and complex effort–especially when an organization has deployed different devices from multiple vendors. When the enterprise has thousands of devices to manage, it’s nearly impossible to keep up–leaving your organization vulnerable to a cyber attack.
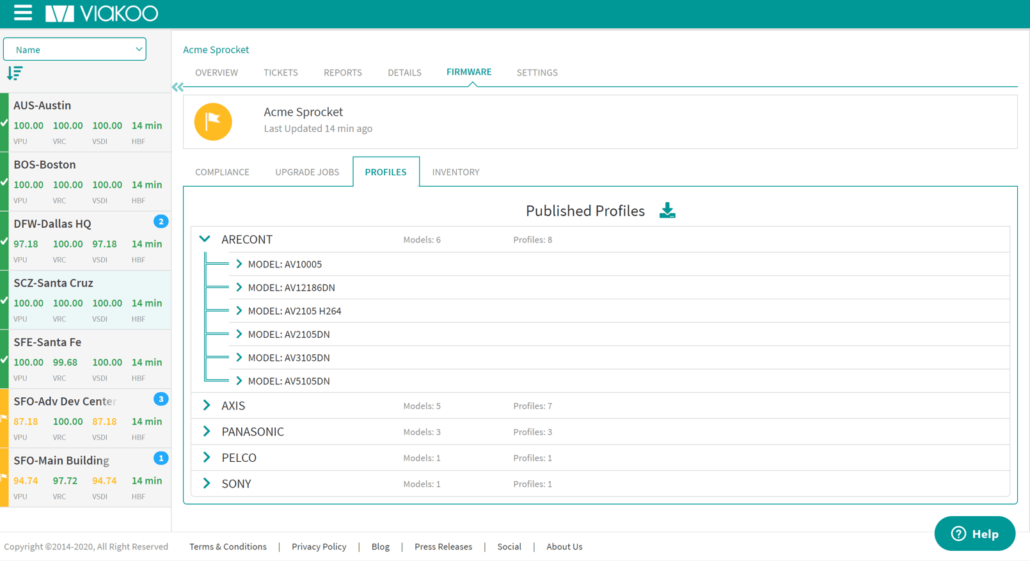
This is where the Viakoo Action Platform with Viakoo DFM delivers. Viakoo not only discovers all your IoT devices, it also determines which ones have old firmware and/or are out of compliance. Best of all, in a few clicks, Viakoo DFM updates them all.
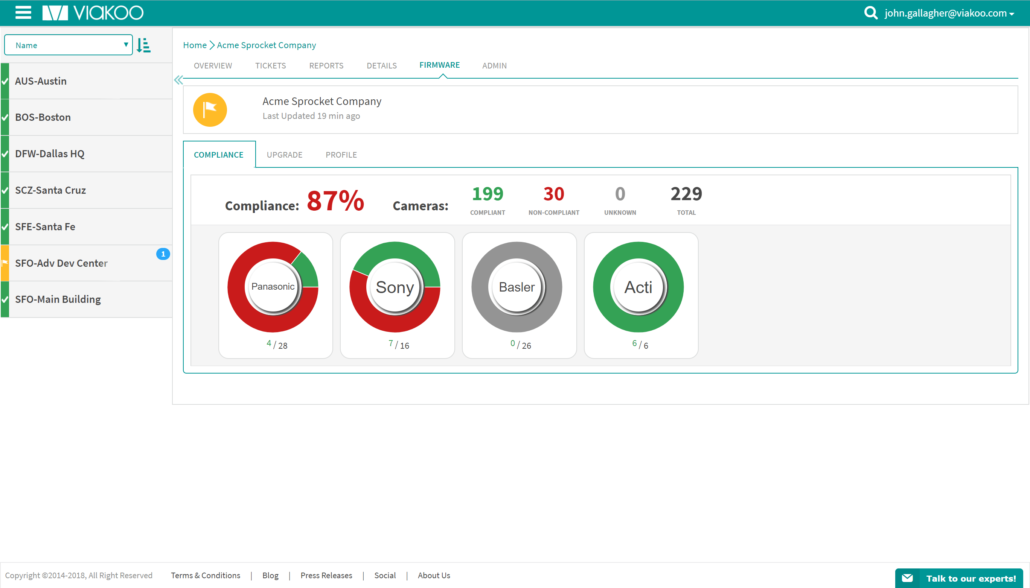
Confirmed Compliance
Once Viakoo Action Platform discovers your IoT devices, it generates a compliance report that clearly displays which devices are compliant with the proper firmware and which ones need upgrades. Viakoo DFM also maintains a history of any changes to device firmware for audit purposes.
Trusted Process
Deploying untrusted or corrupted firmware can turn a useful device into an IT nightmare. Confirming that IoT firmware updates are actually genuine isn’t easy. Viakoo DFM provides a secure “chain-of-trust” method to ensure only valid and functional firmware is deployed. Not only does this provide safety at scale, but it also helps your team be confident in scheduling updates and ensuring IoT devices are operational at all times.
Automated Security
Manually deploying IoT firmware device by device at multiple locations isn’t safe, efficient, or secure. At scale, it is virtually impossible. With a few clicks, Viakoo DFM persistently and automatically updates the firmware of thousands of devices wherever they are—saving time, money, and frustration.
IoT Device Remediation at Scale!
Contact Viakoo for more information!
Let Viakoo prove the value of the Viakoo IoT Management Platform by reducing costs to manage your device firmware, password compliance, and secure certificate management. Viakoo is a 100% AGENTLESS enterprise scale management solution addressing the IoT cyber security needs of all enterprises.
Viakoo’s IoT Firmware Management Solution will scale with your enterprise. With Viakoo, we can prove significant cost reduction, unmatched scalability, a drastic reduction in staffing requirements to manage your devices, and most of all, you will be able to provide an audit trail for compliance that will make any CSO, IT Manager, Risk Manager etc. very happy.
Contact Viakoo for an IoT device risk assessment that will identify your attack surface, today!
Enterprise IoT Firmware Management & Remediation

IoT Device SSL/TLS Certificate Management
Extend Zero Trust coverage to IoT devices with 802.1x / TLS / OPC-UA automated certificate provisioning and management.
Are Your Enterprise IoT Passwords Compliant
Automate verification of password policies at scale and meet standards compliance such as PCI, NERC, and NIST.

Enterprise IoT Device Firmware Management
IoT device security and management with automated firmware updates at an enterprise scale.