When we talk with customers about what is driving them to automate IoT cyber hygiene one topic overshadows everything; shrinking the attack surface that their business-critical IoT systems have become. It makes sense that IoT security has become a priority – compared to other potential attack surfaces in their organization IoT is the fastest growing, the most difficult to manage, involves multiple departments, and exists at a scale anywhere from 5x to 20x traditional IT systems.
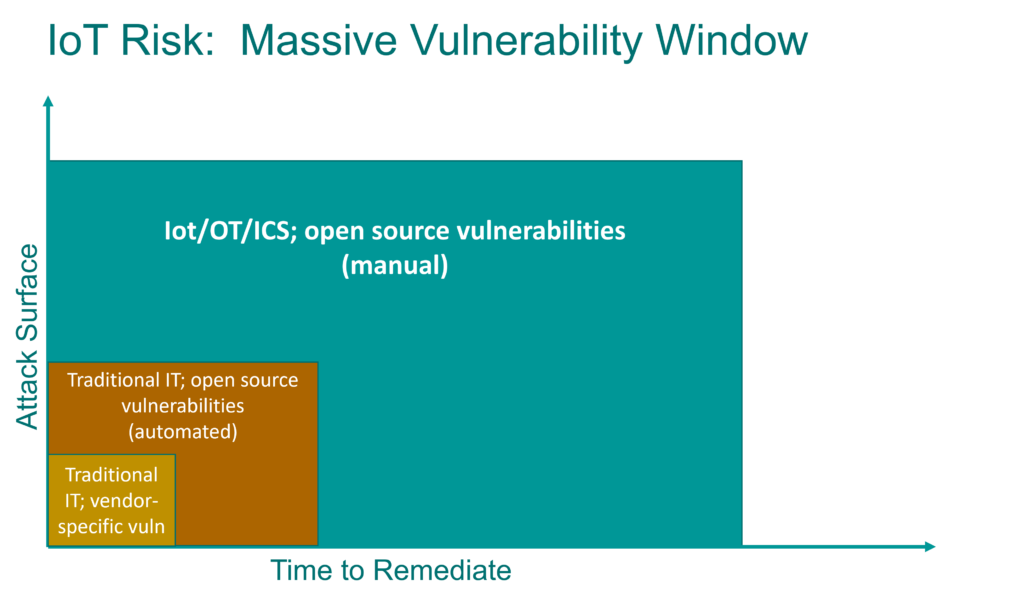
In other words, there is a vulnerability window with IoT that simply dwarfs traditional IT vulnerabilities and how long they exist as a threat. That’s what has created urgency around shrinking that vulnerability window. Viakoo’s focus on automation for firmware, passwords, and certificates is directly aimed at taking the IoT vulnerability window from where it is today (massive) to what it is for traditional IT systems with specific vulnerabilities.
Here are some of the factors that lead to an extended vulnerability window:
1. Open Source Vulnerabilities
It’s notable that that ranking from 2021 to 2022 showed a distinct trend around open source vulnerabilities, specifically SUSE Linux (as well as Ubuntu and Red Hat). This makes remediation much more difficult, as open source distributions can be found in a variety of products, including ones that are not well maintained or hard to patch (like IoT/OT devices).
2. Incorrect CVE scores for IoT
52% of vulnerabilities being incorrectly scored under CVSS v2 scoring. Vulnerability scoring is never fully accurate, as it will not take into account factors that evolve over time, such as exploitability on IoT devices versus IT systems. CVSS v2 was launched in 2007; later versions (specifically CVSS v3.1 that was released in 2019) takes into account more real-life implications of a vulnerability, but still does not account for many IoT/OT/ICS situations. In future versions of CVSS better refinement (especially for IoT/OT vulnerabilities) will help security professional prioritize risk to their organizations more accurately.
3. End of life products
Unlike traditional IT systems, IoT/OT/ICS devices are often viewed as set-it-and-forget-it, including ignoring end of life or end of support dates. Device failure, not manufacturer end of life, often determines when a device is taken out of service.
The good news is that automated methods to address these issues are either here today or close at hand. Organizations need to ensure that their ENTIRE digital landscape is protected and compliant – including IoT/OT/ICS environments that traditionally have been outside the control of corporate security teams. Making sure that all assets are visible, operational, and secure is how organizations need to reassess their security posture – but with a focus on making the “vulnerability window” as short as possible. If you’re not including time to resolution in your security metrics, now is the time to start.





